About the intrusion detection, it is used to discover any illegal or unauthorized computers accessing Enterprise’s internal network. Then we can use the ‘intrusion blocking’ to block any ‘illegal’ computer to access ‘protected’ computers in the network.
For normal use, please see the example below.
Assume we have 2 computers in the network, computer name called Testing and Teclink_demo respectively.
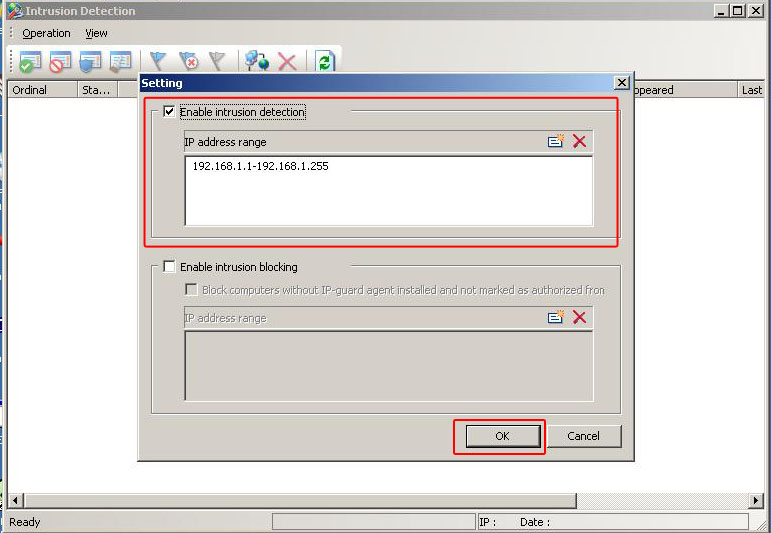
- Choose Tools àIntrusion Detection from the Console menu.
- From the beginning, you should notice there is no computer in the Intrusion Detection windows.
Then check the box ‘Enable intrusion detection’. (If you only want to search specific range, please enter in IP address range, like the picture below)
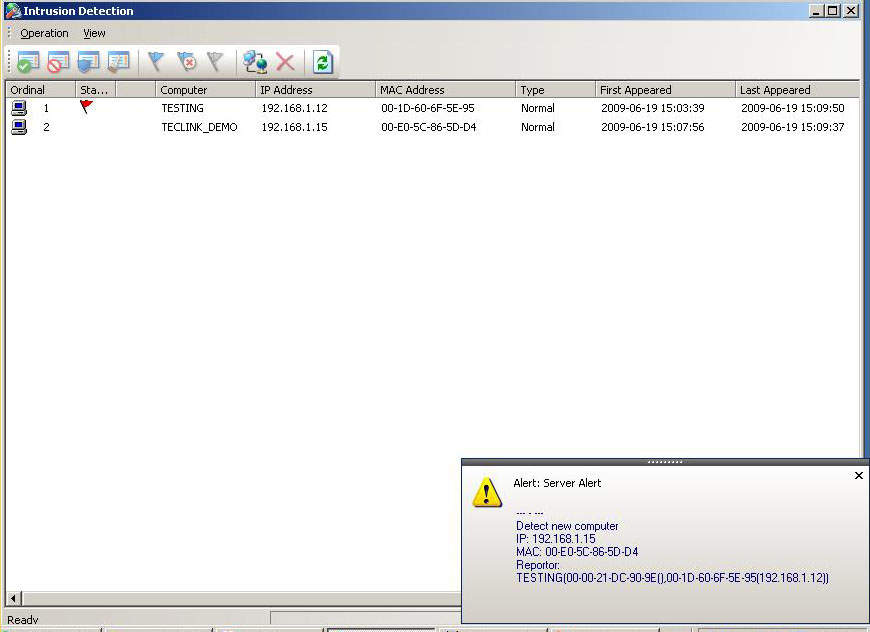
- After clicking OK button, IP-guard will then scan all the computer in the IP address-range just enter (or for whole network if leaving blank)
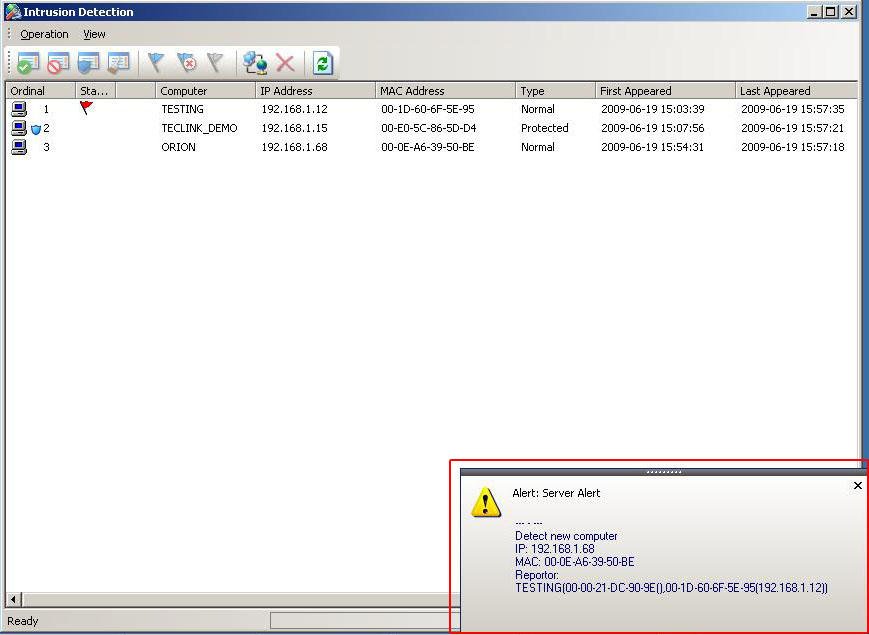
- Then, after all computer scanned, the alert message appear for any new computer and you can see the list of the computer, like the picture below.
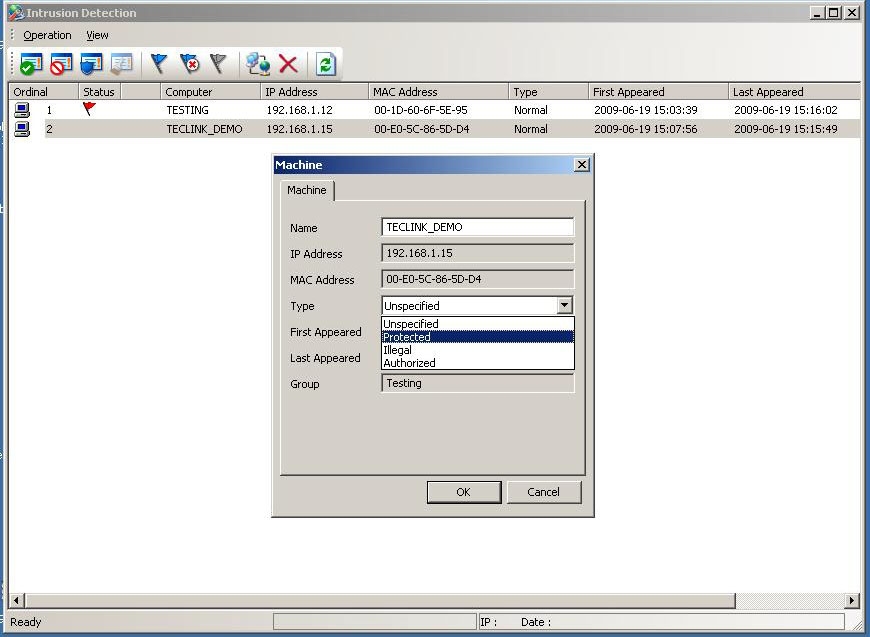
- Then for every computer you want to protect, double-click it and then set it as ‘Protected’ type and click OK, like the picture below.
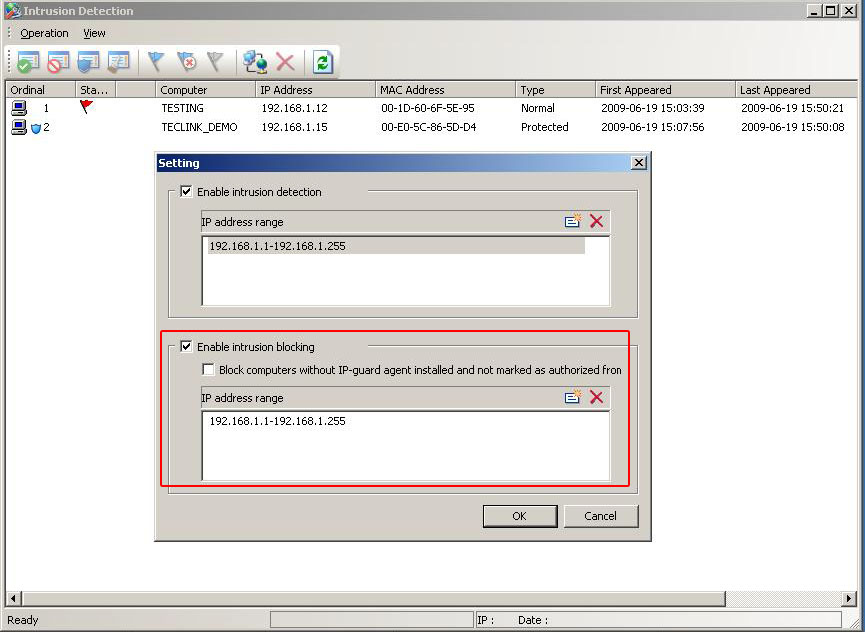
- After all computers you want to protect set as ‘protected’, choose Operation -> Settingfrom the Intrusion Detection window menu.
- Then if any ‘un-authorized’ computer plug into this network (eg. user plug-in a notebook computer newly to the network).
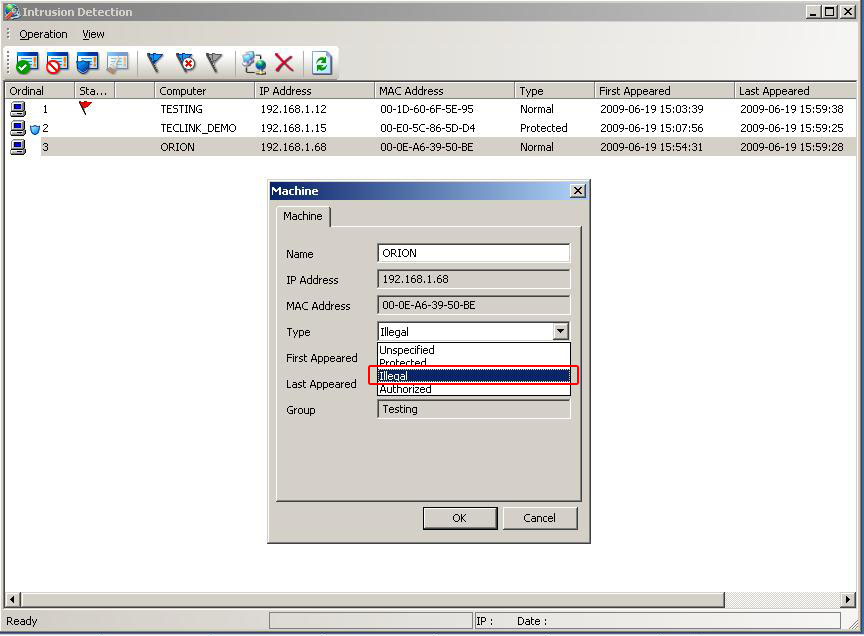
- Then you double-click this ‘un-authorized’ computer in the Intrusion Detecton window, and set it type as ‘Illegal’.
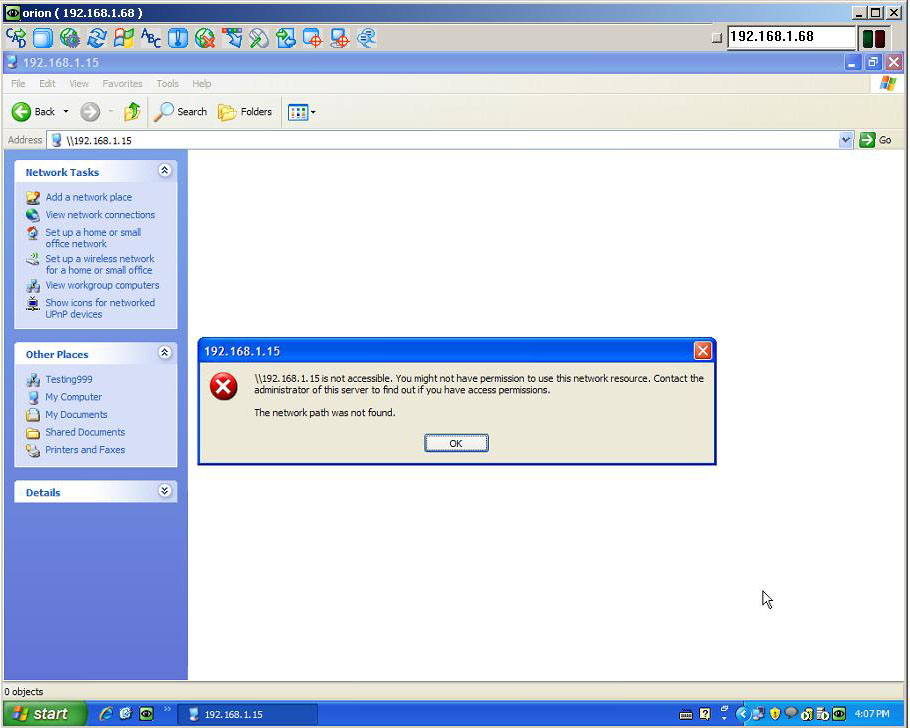
- After the policy is updated, in that ‘un-authorized’ computer (eg. ORION), no communication is allowed between it and to the ‘protected’ type computer.
For detail explanation of each field, please refer to the section 10 of the user manual:
http://www.ip-guard.com/public/user_manual/v1.0/IP-guard_UserManual_EN_v1.0_Rev20090623.pdf
